Imagine trying to steal from a vault where the only way to get inside is to spend billions of dollars on electricity and hardware, and the moment you succeed, the vault's value might vanish because everyone knows you've cheated. It sounds like a bad deal, right? That is exactly how Proof of Work is a cryptographic consensus mechanism that requires participants to spend computational energy to validate transactions works. It isn't just a technical quirk; it is an economic firewall that makes attacking Bitcoin prohibitively expensive.
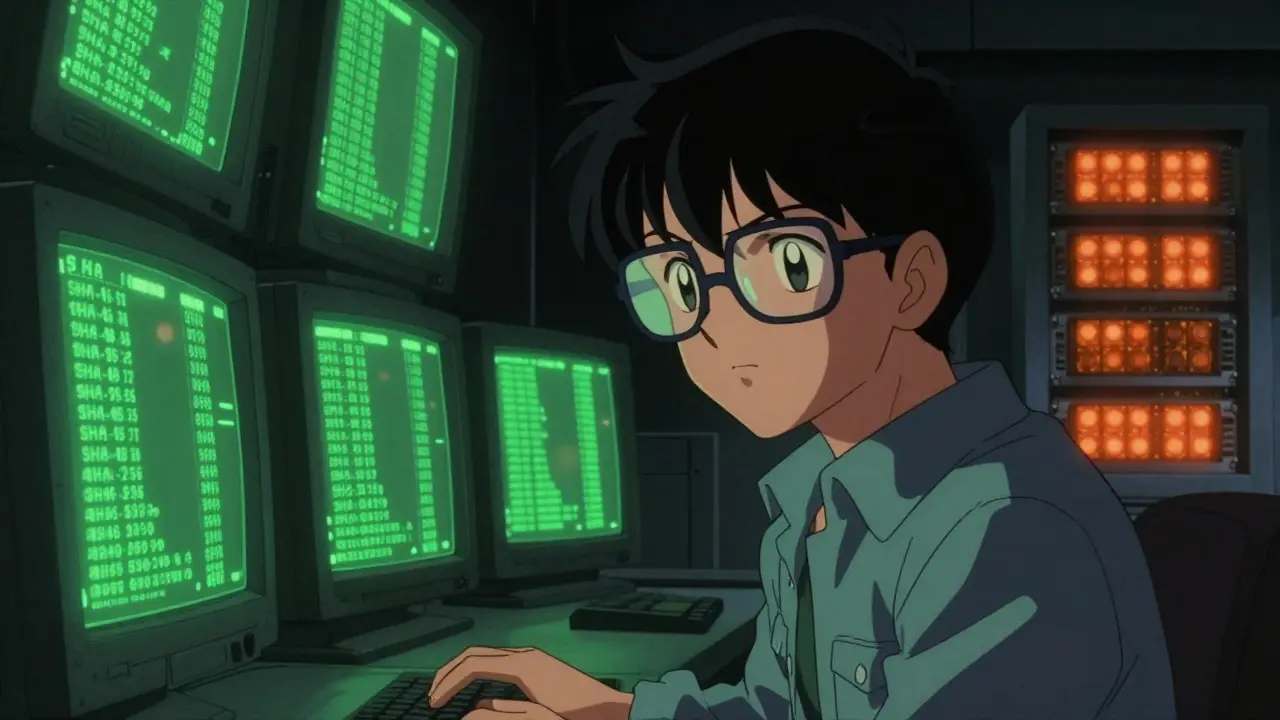
The Heavy Lifting of SHA-256
At the heart of Bitcoin's security is the SHA-256 a cryptographic hash function that turns any input into a unique 256-bit string of characters algorithm. Think of this like a digital fingerprint. If you change one single comma in a thousand-page document, the SHA-256 hash changes completely. To mine a block, miners have to guess a number (called a nonce) that, when combined with the block data, produces a hash with a specific number of leading zeros.
This is a game of pure chance and brute force. As of late 2023, the network difficulty was around 83.15 trillion, meaning miners had to find a hash with 19 leading zeros. There is no shortcut, no "hack," and no way to predict the result. The only way to find the answer is to try trillions of combinations per second. This process ensures that adding a block to the chain requires a verifiable amount of physical work-specifically, electricity and heat.
Why Electricity Equals Security
You might wonder why spending so much energy is a good thing. In the digital world, things are easy to copy. If Bitcoin used a simple voting system, a hacker could just create a million fake accounts (a Sybil attack) to outvote everyone else. Proof of Work stops this by tying the right to vote to a physical resource: energy.
By requiring miners to burn electricity, Bitcoin creates a cost asymmetry. For an attacker to rewrite the history of the blockchain, they would need to control more than 50% of the total computing power-known as a 51% attack. With the global hashrate reaching 600 exahashes per second, the sheer amount of hardware and power needed is staggering. According to data from River Financial, sustaining such an attack would cost roughly $15.8 billion every single month. When the cost of the attack is higher than the potential loot, the system is secure.
| Feature | Proof of Work (Bitcoin) | Proof of Stake (Ethereum) |
|---|---|---|
| Resource Required | Physical (Electricity/ASICs) | Virtual (Staked Tokens) |
| Attack Cost (Est.) | ~$28 Billion (Initial) | ~$18.6 Billion |
| Energy Use | High (TWh/year) | Very Low (GWh/year) |
| Security Basis | External cost of energy | Internal value of tokens |
Solving the Byzantine Generals Problem
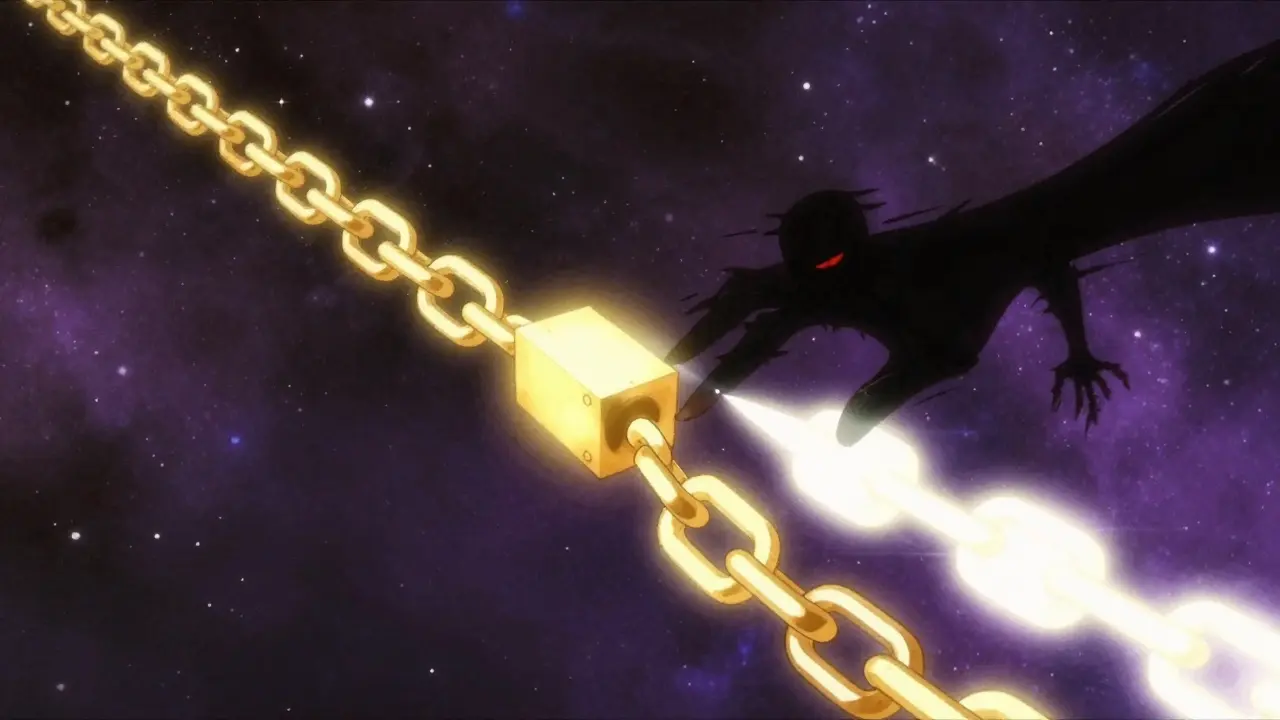
In a decentralized system, how do you know which version of the truth is correct when there is no boss in charge? This is the classic Byzantine Generals Problem. Bitcoin solves this by following the "longest chain" rule. Because every block contains the hash of the one before it, they are linked like a physical chain. If you want to change a transaction in block 100, you have to re-mine block 100, 101, 102, and every block after it.
Because the rest of the network is still mining forward on the original chain, the attacker has to work faster than the entire rest of the world combined to catch up. Since the Blockchain a distributed ledger that records all transactions across a network of computers is public, everyone can see that the attacker is trying to create a fraudulent fork, and the honest nodes will simply ignore it.
The Hardware Race: ASICs and Specialization
In the early days, you could mine Bitcoin with a home PC. But as the network grew, miners started using ASICs Application-Specific Integrated Circuits designed specifically for mining cryptocurrency. These are machines that do nothing but calculate SHA-256 hashes. This specialization has pushed the security even higher.
When you buy an Antminer S19 XP, you are investing in a machine that is useless for anything other than mining. This "sunk cost" aligns the miner's interests with the network's health. If a miner tries to attack the network, the value of Bitcoin would likely crash, making their multi-million dollar investment in hardware worthless overnight. It is much more rational to earn the block reward-which was 6.25 BTC before the April 2024 halving-and the accompanying transaction fees.
Common Myths and Realities
The most common criticism of PoW is its environmental impact. While it is true that Bitcoin uses a lot of power-roughly 121.49 terawatt-hours annually-it is important to look at where that power comes from. The Bitcoin Mining Council reported that about 48.1% of mining energy comes from renewable sources. In many cases, miners use "stranded" energy, like remote hydroelectric dams that produce more power than the local town can use.
Some argue that Proof of Stake is "better" because it is greener. While PoS (like Ethereum) is indeed more efficient, it replaces physical energy with financial stakes. This creates a different kind of risk: the rich get richer, and those with the most tokens have the most control. Bitcoin's PoW remains a more objective system because you cannot "cheat" the laws of physics or the cost of electricity.
What happens during a 51% attack?
In a 51% attack, a person or group controls more than half of the network's mining power. They can't steal your coins out of your wallet, but they could potentially reverse their own recent transactions (double-spending) or stop other transactions from being confirmed. However, the cost to do this on Bitcoin is so high that it is economically irrational.
Why does the difficulty adjust every 2,016 blocks?
Bitcoin is programmed to produce a block roughly every 10 minutes. If more miners join and the hashrate increases, blocks would be found too quickly. To prevent this, the network automatically makes the math puzzle harder every 2,016 blocks to keep the timing consistent.
Does the halving affect security?
The halving reduces the new BTC reward for miners. Some worry this lowers security because miners earn less. However, as the price of Bitcoin rises, the transaction fees paid by users help fill the gap, keeping the "security budget" high enough to attract miners.
Can someone use a supercomputer to break SHA-256?
Current supercomputers are not designed for the specific repetitive hashing that SHA-256 requires. ASICs are far more efficient. Even with a supercomputer, the sheer number of guesses required to find a valid hash is so astronomical that it remains computationally infeasible.
Is Proof of Work better than Proof of Stake for a reserve asset?
For an asset intended to be a "global reserve," security and immutability are more important than transaction speed. PoW's reliance on real-world energy makes it harder to manipulate via social engineering or financial collusion, which is why many experts prefer it for long-term value storage.
Next Steps for Understanding Bitcoin
If you want to go deeper into how this all fits together, start by looking into the Nakamoto Coefficient to see how decentralized the mining pools actually are. From there, explore how Taproot updated Bitcoin's privacy without touching the PoW layer. If you're feeling adventurous, you can even set up a "node" at home to verify the blocks yourself and see the consensus process in real-time.