When you interact with a dApp - whether swapping tokens on a decentralized exchange, buying an NFT, or voting in a DAO - you’re trusting code that runs on a public blockchain. There’s no customer support line. No password reset. No central authority to reverse a mistake. If something goes wrong, your funds are gone. And it’s not just users at risk. Developers who skip basic security steps are building digital landmines.
Smart contracts aren’t just code - they’re digital banks
Most dApp vulnerabilities come from the smart contract layer. These are self-executing programs on blockchains like Ethereum, and they hold real value. A single line of flawed code can drain millions. The OWASP Smart Contract Security Verification Standard (a draft standard released in September 2024 to define secure practices for EVM-based dApps) lists the most common flaws: reentrancy attacks, integer overflows, unchecked external calls, and improper access control.Reentrancy is the classic example. Imagine you withdraw $100 from an ATM, but before the machine dispenses cash, you quickly trigger the same withdrawal again - and again - until the account is empty. That’s exactly what happened in the 2016 DAO hack, where attackers reused a function call to drain $60 million. Modern tools like Slither and MythX can detect these patterns, but many dApps still skip audits entirely. A 2024 report showed that 43% of newly launched DeFi protocols had no public audit report.
Always verify that a dApp’s contract has been audited by a reputable firm - not just a one-time check, but a recent one. Look for the auditor’s name on Etherscan or the project’s GitHub. If it’s missing, treat it like a website with no SSL certificate: don’t trust it.
Frontend tricks and wallet traps
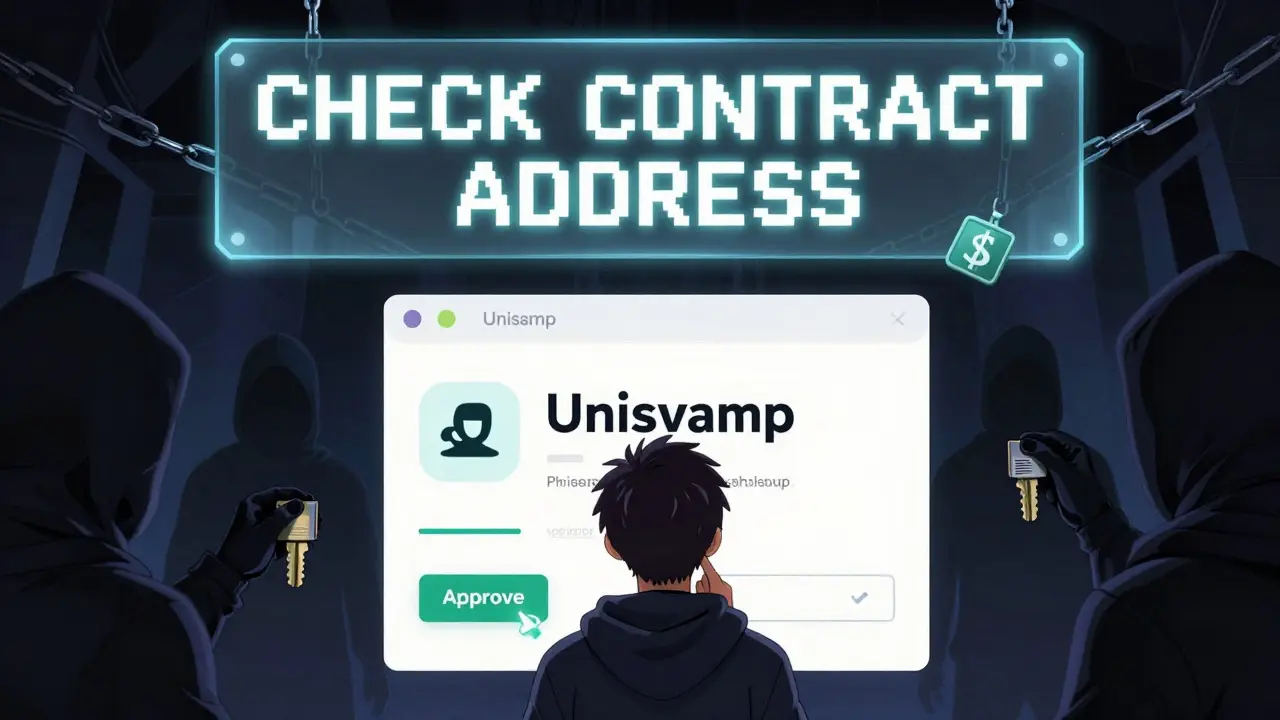
Even if your smart contract is bulletproof, your frontend can still get you hacked. Most dApp attacks don’t target code - they target users. Phishing sites look identical to Uniswap, OpenSea, or MetaMask. They trick you into signing malicious transactions that give attackers full access to your wallet.Here’s how to spot the red flags:
- Always double-check the contract address before approving a transaction. Copy-paste it from the official website - don’t trust links in Discord or Twitter DMs.
- Never sign a transaction unless you understand what it’s doing. A "Approve" button on a fake DEX might let someone drain your entire balance, not just one token.
- Use wallet interfaces that show full transaction details: token amounts, fees, and the target contract. MetaMask and Rabby Wallet now highlight suspicious approvals with warnings.
- Enable transaction delays or multi-signature approvals if your wallet supports it. This gives you a buffer to cancel if something feels off.
Many NFT marketplaces still let users approve unlimited token spending - a dangerous default. Always set spending limits per contract, and revoke approvals you no longer use. Tools like Revoke.cash make this easy.
Decentralization isn’t magic - it’s a design choice
A dApp isn’t truly decentralized just because it runs on a blockchain. Many still rely on centralized servers for their frontend, user authentication, or data storage. If the backend server goes down, the dApp breaks. If the company behind it gets hacked, your data is exposed.True decentralization means:
- The frontend is hosted on IPFS or Arweave, not a cloud provider like AWS.
- Core functions are controlled by smart contracts, not a single developer’s key.
- Upgrades require community approval via governance votes, not a CEO’s decision.
Some projects use Service Nervous System (SNS) (a decentralized governance system on the Internet Computer that allows dApps to be controlled by token holders, not developers) to hand over control to users. Others use Orbit Station (a canister-based enterprise wallet tool for managing multi-signature policies on the Internet Computer) to require multiple approvals for critical changes.
If a dApp’s admin key is held by one person, treat it like a bank with a single employee holding all the vault keys. That’s not decentralization - it’s a single point of failure.
Privacy isn’t optional - it’s structural
Blockchains are public ledgers. Every transaction you make is visible forever. That’s fine for payments, but terrible for identity. If you’ve ever connected your wallet to a dApp and later realized your entire trading history is public, you know the risk.Modern dApps are starting to use:
- Zero-knowledge proofs (a cryptographic method that lets you prove you own something without revealing what it is - for example, proving you have enough tokens to trade without showing your balance)
- Decentralized identity (DID) (user-controlled digital identities that let you prove attributes like age or KYC status without sharing personal data)
- Gateway Protocol (a permission layer that lets users control exactly what data they share with each dApp)
Imagine logging into a dApp and only revealing your wallet address - nothing else. No email, no name, no transaction history. That’s the future. Projects like Worldcoin and Polygon ID are already testing this. If a dApp asks for your real name or phone number without a clear reason, walk away.
Security is a habit, not a one-time fix
You wouldn’t leave your front door unlocked just because you installed a fancy alarm. The same applies to dApps. Security isn’t a checkbox. It’s ongoing.For developers:
- Use formal verification tools like Certora or Foundry to mathematically prove contract behavior.
- Run automated scans daily with Slither or MythX.
- Keep dependencies updated. A single outdated library like OpenZeppelin v3.0 can expose you to known exploits.
- Implement role-based access control. Only admins should be able to pause contracts or change fees.
For users:
- Use a separate wallet for dApp interactions - never your main wallet with all your ETH or BTC.
- Enable 2FA on your wallet provider.
- Never share your seed phrase. Not even with "support".
- Check the dApp’s GitHub. Are commits frequent? Are issues being addressed? Silence is a red flag.
Remember: no dApp is 100% secure. But many are dangerously careless. Your responsibility doesn’t end when you click "Connect Wallet". You’re now part of the security chain.

Common threats you can’t ignore
Here are the real-world dangers you’re most likely to face:- Rug pulls: Developers abandon a project after draining liquidity. Look for locked liquidity and community-owned contracts.
- Front-running: Miners or bots see your trade and execute theirs first to profit. Use limit orders and avoid high-traffic swaps.
- Malicious token approvals: A fake token asks you to approve unlimited spending. Always check the token contract address before approving.
- Man-in-the-middle attacks: Fake browser extensions or compromised devices intercept your wallet signatures. Only install extensions from official sources.
Most of these are preventable with awareness. The biggest threat isn’t hackers - it’s complacency.
What you should do today
If you’re a developer:- Run your smart contract through Slither or MythX.
- Get a third-party audit from a known firm like CertiK, Trail of Bits, or OpenZeppelin.
- Host your frontend on IPFS.
- Use SNS or multi-sig for governance.
If you’re a user:
- Check if the dApp has a public audit report.
- Verify the contract address on Etherscan or the official site.
- Use a dedicated wallet for dApps.
- Revoke unused token approvals with Revoke.cash.
- Never click on wallet connection links from DMs or unverified sources.
Security in Web3 isn’t about perfection. It’s about layers. Every step you take - from auditing code to checking addresses - reduces your risk. The more you know, the less likely you are to become a statistic.
Are dApps safer than traditional apps?
dApps aren’t inherently safer - they’re just different. Traditional apps have centralized servers you can sue if hacked. dApps have code you can’t change if broken. The trade-off is control: you own your data and funds, but you’re also fully responsible for security. A well-built dApp can be more secure than a poorly secured bank app, but most dApps today are far from well-built.
Can I recover funds if I send them to the wrong dApp address?
No. Blockchains are immutable. Once a transaction is confirmed, it can’t be reversed. There’s no customer service, no chargeback, no reset button. That’s why verifying addresses is non-negotiable. Always copy-paste contract addresses from official sources - never type them manually.
What’s the biggest mistake new dApp users make?
Signing transactions without understanding what they do. Many users click "Approve" because they see a familiar interface - but that approval might give a hacker full access to their wallet. Always read the transaction details: what contract are you interacting with? What permission are you granting? If you don’t know, don’t sign.
Do I need a hardware wallet for dApp security?
Not always, but it’s highly recommended if you hold significant value. Hardware wallets like Ledger or Trezor keep your private keys offline, protecting them from malware and phishing. For small, frequent transactions, a software wallet with strong 2FA is acceptable. For large holdings or DAO participation, hardware is the baseline.
How often should I check my token approvals?
Every 3 to 6 months. Many users approve unlimited spending for convenience - then forget about it. A hacker only needs one old approval to drain your wallet. Use Revoke.cash or your wallet’s built-in approval manager to review and revoke unused permissions regularly.
Is open-source code enough to trust a dApp?
No. Open-source code is necessary, but not sufficient. Anyone can publish code. What matters is whether it’s been audited, tested, and actively maintained. Check commit history, issue responses, and audit reports. A project with zero commits in 6 months is dead - even if the code is "open".
What’s next?
The dApp security landscape is evolving fast. The OWASP SCSVS draft is a major step toward standardization. Hardware security modules like YubiHSM are becoming more accessible to developers. Zero-knowledge tech is moving from theory to real-world use in privacy-focused dApps.But the biggest change won’t come from tools - it’ll come from mindset. Security in Web3 isn’t something you outsource. It’s something you practice daily. Whether you’re coding or just clicking "Connect Wallet," you’re responsible for your own safety. The blockchain doesn’t care if you made a mistake. It only records it.
